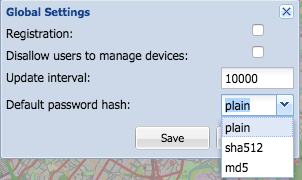
Have you ever wondered why when you no longer remember the password of a website, you are never allowed to recover it, but only to reset it? The answer is simple: the administrators don’t even know it! Whenever you access a web application, for example, your Facebook, Google, Yahoo, and Twitter account and so on, you get authentication only if the password you entered matches the one stored in the system. The passage just described takes place in a few tenths of a second and the passwords compared, due to a security issue, are never in the clear, as they undergo a process known as hashing that varies according to the cryptographic algorithm used. From Ciphra this is the best option now.
In small words, this type of encoding takes as input a variable length strings your password and returns the output, also known as MD5 Checksum. It is not possible to trace what originated from a hash thus obtained.

Differences between hashing and cryptography
Hashing and encryption are different ways of protecting information. Encryption allows you to restore the original text later by decoding. Hashing sums up the text in a short print that cannot be decrypted. With the hash print alone, there is no way of knowing exactly which text was summarized even if a given the word always generates the same footprint. In doing so, if an attacker were able to obtain the database of a website containing all the “hash” passwords of the registered users, a pile of 128-bit strings consisting of 32 hexadecimal characters would be in hand. Follow the next example to better understand this mechanism.
Hash, insights and practical examples
The turn hacker gets the hash of the Banda Bassotti password which during registration has chosen the keyword “password123” which through the MD5 hashing process corresponds to the value. There are hundreds of sites that contain billions of terms in their databases in all the “pre-hash” languages and in the blink of an eye they search for the output entered, and if they find a match, they return the word in clear text. You can make a quick check by visiting the website md5online.org, which contains almost 125 billion terms. Copy and paste the above string in the appropriate field of the mentioned site and click on Decrypt.
Salt, this stranger
To prevent this type of attack, in English called the Rainbow Table, a gimmick was introduced: the salt. The latter is nothing more than a random bit sequence used by the server to obtain a unique output during the password hashing process; When logging in, the password entered is again combined with the seed and the string obtained is compared with that stored in the website database and if the values coincide, the user has access to the system.
If the company during registration had benefited from this arrangement, and the server had used the value sale321 as a salt, the secret key chosen by him, or the word password123, would have produced an output that could no longer be calculated using the use of the Rainbow Tables and in this case the result obtained by this irreversible mathematical function would have led to differences.